Russian State, Criminal Links Still Elusive
PLUS: What Hive and Alphabay (Hopefully) Have in Common
Your weekly dose of Seriously Risky Business news is written by Tom Uren, edited by Patrick Gray with help from Catalin Cimpanu. It's supported by the Cyber Initiative at the Hewlett Foundation and founding corporate sponsor Proofpoint.
Russian State, Criminal Links Still Elusive
It's clear there are some tenuous connections between Russian intelligence services and criminal groups operating from within the country, according to a report from threat intelligence company Recorded Future.
The company published a report on this purported collaboration in September 2021 and this week's follow-up report, Dark Covenant 2.0, focuses on events that occurred after Russia's invasion of Ukraine began.
The two reports collate a lot of circumstantial evidence pointing to possible links between the Russian state and its cybercriminals. Based on this evidence, one of the report's key judgements is that:
It remains highly likely that Russian intelligence, military, and law enforcement services have a longstanding, tacit understanding with cybercriminal threat actors; in some cases, it is almost certain that these agencies maintain an established and systematic relationship with cybercriminal threat actors, either by indirect collaboration or via recruitment.
The report does a terrific job of pulling together a lot of circumstantial evidence, but concludes with a pretty bold claim. We don't think they've been able to demonstrate that these "established and systematic" relationships are particularly deep.
One direct link between Russian intelligence services and the criminal community the report cites is the recruitment of criminal hacker Dmitry Dokuchaev into the FSB. There have also been times that the GameOver Zeus Botnet, a criminal botnet run by Evgeniy Bogachev, was used to search for documents marked with keywords such as "top secret" or "security service of Ukraine," for example.
The report cites a New York Times article that quotes a Ukrainian Interior Ministry file on Bogachev. The file says Bogachev was "working under the supervision of a special unit of the FSB". The article doesn't give us any indication of how Ukrainian authorities arrived at this conclusion, so our inclination is to treat this claim carefully.
The keyword searches could suggest intelligence service-directed tasking. But they could also just indicate that Bogachev is a curious person, or that he wanted to have some useful information up his sleeve if he ever had problems with the FSB.
As for Russia's "hacktivists," on at least four occasions, Russian hacktivist groups such as Xaknet have leaked data from Ukrainian wiper victims within 24 hours of a destructive attack, the report says. This suggests that Russian authorities, at the very least, know how to get in touch with these groups. Then again, we doubt contacting them via Telegram would be particularly difficult.
There are other overlaps too, but for many of them it's hard to know whether they are the result of deliberate coordination or merely an alignment of interests.
Overall the report leaves us with the conclusion that there are some tenuous links, but we don't know how extensive they are.
But whatever conclusions we've drawn from Recorded Future's report, it's definitely worth a read. They've pulled together an awful lot of information and put it in one place, and that's very useful.
What Hive and Alphabay (Hopefully) Have in Common
Last week the FBI announced the conclusion of a months-long disruption campaign targeting the Hive ransomware group that culminated in the seizure of the group's servers.
Hive was the world's most commonly deployed ransomware strain.
In addition to seizing control of the IT infrastructure that Hive used to communicate with its members, the FBI had been passing decryption keys to Hive victims for several months. From the FBI's press release:
Since late July 2022, the FBI has penetrated Hive’s computer networks, captured its decryption keys, and offered them to victims worldwide, preventing victims from having to pay $130 million in ransom demanded. Since infiltrating Hive’s network in July 2022, the FBI has provided over 300 decryption keys to Hive victims who were under attack. In addition, the FBI distributed over 1,000 additional decryption keys to previous Hive victims.
In our most recent edition, we argued that ransomware crews were "ripe for disruption" and this is an excellent real-world example of how these operations can be carried out. It appears that there was at least some hacking involved, although it's not clear exactly what went on.
At the Department of Justice press conference announcing the takedowns, US Deputy Attorney General Lisa Monaco said, "simply put, using lawful means, we hacked the hackers".
FBI Director Christopher Wray shed a little more light. "Last July", he said, "FBI Tampa gained persistent clandestine access to Hive's control panel and since then for the past seven months we've been able to exploit that access while keeping Hive in the dark".
The speakers at the press conference — which included an appearance from US Attorney General Merrick Garland — hit on the importance of international collaboration and the creative use of both criminal and civil authorities. They also highlighted the value of disrupting the ransomware group's operations, even if no arrests were made.
There were some equities to balance here.
It can't have been easy for the FBI to figure out exactly when to drop the hammer on Hive. Being able to provide decryption keys to the group's victims was a fantastic position to be in. That said, ransomware recovery — even when you have the keys — is arduous. It took the Irish Health Service months to recover from a Conti ransomware attack even after the group provided it with a free decryption key.
So the FBI actually sharing this information with victims marks a shift in policy. In July 2021, the FBI gained access to REvil's decryption key in the aftermath of its attack on Kaseya customers, but decided not to pass it on to avoid spooking REvil prior to an impending takedown operation.
In the end, REvil's sites disappeared before the operation could be carried out, so withholding the decryption key turned out to be pointless.
So it's clear the FBI's approach to running these types of operations — and the way it weighs up competing equities — is still evolving. One extremely positive (in our view) development is the FBI's embrace of a disruption model as opposed to an arrests-as-the-win model.
And yes, a lot of the group's affiliates will now scurry off towards other RaaS groups where the FBI may not have visibility. But there's every chance that the agency or its partners have already infiltrated at least some of these other groups. That would be quite funny.
We've seen that sort of thing before. When the FBI shuttered the Alphabay dark web marketplace, Dutch authorities had already secretly taken over its primary competitor, Hansa. Alphabay users flocked to Hansa in the wake of the takedown and hilarity ensued.
In short, now the FBI and its partners have a template for disrupting ransomware groups we can expect to see it happen more often. This is hopefully just the beginning.
USA and Singapore Target Robocallers, Scam SMSs
Robocallers and SMS scammers have been put on notice in the United States and Singapore, and the contrast in the two government's approaches to these similar problems are pretty interesting.
In the US, the Federal Communications Commission (FCC) issued a Robocall Enforcement Notice ordering US-based voice service providers to stop carrying illegal robocalls from US company MV Realty. The FCC specifically called out US-based communications company Twilio, issuing it a cease and desist letter asking it to "effectively mitigate", i.e. block, the traffic from MV Realty.
Twilio received the letter because one of its clients, PhoneBurner, was initiating calls on Twilio's networks for MV Realty. MV Realty was not only making unsolicited calls to numbers on the national Do Not Call registry (nearly 12 million of them), but is also being sued by three state Attorneys General for alleged mortgage scams.
The letter included a big, fat warning: "Failure to comply with the steps outlined in this letter may result in downstream voice service providers blocking all of Twilio’s traffic, permanently."
The FCC has issued Robocall Enforcement Notices before, but this action is significant in a couple of ways. Firstly, Twilio is the largest voice service to receive a cease and desist letter from the FCC and previous letters haven't gone to big industry players. Secondly, Twilio is being held accountable for the actions of one of its clients, with the FCC implying that Twilio should conduct more Know Your Customer due diligence to proactively prevent this kind of traffic. In the FCC's press release about the action, its Enforcement Bureau Chief Loyaan A. Egal is quoted saying that "'Know Your Customer' (KYC) principles should be at the forefront of all communications service providers' business practices".
This makes sense — rather than cutting off robocalls after they've caused problems it's better to stop them in the first place. So the FCC is sending a pretty strong message to encourage service providers to pay more attention to what their customers are doing.
In Singapore, the government has taken a different approach when it comes to mitigating SMS scam messages — rather than pushing efforts to the private sector it is taking a more centralised and government-led action.
One initiative is to require registration before organisations can use SMS Sender IDs, personalised alphanumeric sender IDs. From the beginning of this month messages from organisations that aren't registered will now be labelled as being sent from "Likely-SCAM" to alert consumers. The government plans to block unregistered numbers after six months.
Since October last year, the government has also required that telcos scan for malicious SMS messages and block them. This is based on the detection of malicious links and the filtering of messages that contain "suspicious patterns". Amazingly, Singapore's government authority issued the decision to implement an SMS anti-scam filter on the 14th of October and ordered that it be implemented by the 31st of October!
Although the US and Singapore government efforts to cut down on scams are implemented very differently, they are both trying to achieve essentially the same goal. That is, to direct the organisations that have a privileged position in the network to detect and block scam messages.
Three Reasons to be Cheerful this Week:
International Counter Ransomware Task Force starts: Australia commenced operations of the task force at the beginning of last week. The idea is to "drive international cooperation to tackle ransomware, including through information and intelligence exchanges, sharing best practice policy and legal authority frameworks, and collaboration between law enforcement and cyber authorities".
Ukraine to join NATO Cyber Defence Centre: Ukraine has signed an agreement to join the Estonia-based NATO Cooperative Cyber Defence Centre of Excellence (CCDCOE). Although the CCDCOE is a NATO organisation, Ukraine becomes one of nine non-NATO "contributing participants" which include Australia, Japan and South Korea. The Record has more on the agreement.
RSOCKS Proxy Botnet Administrator Guilty: Denis Emelyantsev pled guilty in California to computer crime charges. Emelyantsev ran the RSOCKS botnet and sold access to compromised devices as proxy servers for criminals looking to route traffic through someone else's device.
Sponsor Section
Seriously Risky Business is supported by the Hewlett Foundation's Cyber Initiative and corporate sponsor Proofpoint.

Okta and Passwordless Authentication
Risky Business publishes sponsored product demos to YouTube. They're a great way for you to save the time and hassle of trying to actually get useful information out of security vendors. You can subscribe to our product demo page on YouTube here.
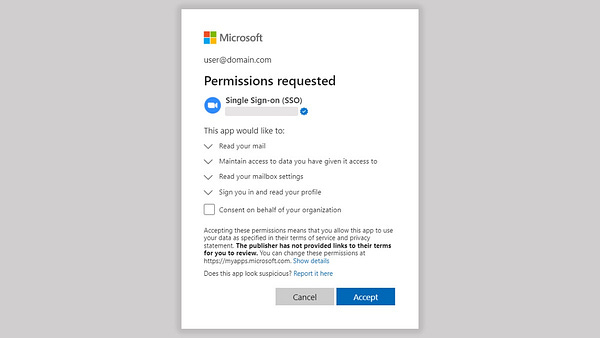
In our latest demo, Brett Winterford and Harish Chakravarthy demonstrate to host Patrick Grey how Okta can be used for passwordless authentication. These phishing resistant authentication flows — even if they are not rolled out to all users — can also be used as a high-quality signal of phishing attempts that can be used to trigger automated follow-on actions.
Shorts
Good News, Bad News
Ransomware incident response firm Coveware reports that fewer victim organisations are paying ransoms. Last quarter only 37% of victims paid, down from a staggering 85% in the first quarter of 2019.
Coveware attributes this to a few key factors: Enterprise security and backups are better these days, law enforcement is doing a better job, and the criminal ransomware ecosystem is shrinking. Less money has meant fewer criminals which means fewer ransomware incidents.
That's almost too much optimism for this newsletter. To balance it out, Coveware also reports that ransomware actors are targeting bigger companies, getting bigger ransom payouts, and even re-extorting victims. That is, they are demanding a second ransom payment after an initial ransom is paid.
TikTok has a Plan
TikTok is on a charm offensive, actively spruiking its plans to mitigate concerns that it will spy on or influence US audiences. The company has briefed the Committee on Foreign Investment in the United States (CFIUS), academics, think tankers and others. Here is a summary from Klon Kitchen on Twitter, and here is a deeper dive on Lawfare.
We've covered some of these potential risks before and we still think successfully isolating US TikTok from its Chinese parent company ByteDance — and therefore PRC government influence — will be very difficult. TikTok says it will create a new unit, TikTok US Data Security, with 2,500 US-based engineers, security experts and trust and safety officials, but apart from the hiring blitz we don't really see anything new here.
Under New Management
Proofpoint has released a report on a state-sponsored North Korean group it calls TA444 that is all about stealing money for the regime. TA444 overlaps with APT38 and Stardust Chollima and has recently adopted a "startup" attitude where it is willing to adopt and experiment with new techniques that are used by other threat actors. We wonder if it has new management.
Proofpoint is a corporate sponsor of this newsletter.
Risky Biz Talks
In addition to a podcast version of this newsletter (last edition here), the Risky Biz News feed (RSS, iTunes or Spotify) also publishes interviews.
In our last "Between Two Nerds" discussion Tom Uren and The Grugq look at operations being ‘burnt’ from the adversary’s point of view. What do they do when an operation is burnt? What are the factors that go into the decisions that they make?
From Risky Biz News:
Criminal money laundering: Blockchain analysis company Chainalysis says that 67.9% of the $23.8 billion worth of cryptocurrency linked to illicit addresses last year has passed and been laundered through one of five major cryptocurrency exchanges. In an exclusive with Wired, Chainalysis declined to name the five exchanges.
FBI links Harmony's $100 million hack to the Lazarus Group: The FBI has formally attributed the hack of the Harmony cryptocurrency bridge platform to Lazarus, a cyber-espionage group working for the North Korean government. (much more at Risky Biz News).
Crypto-crime volumes went down in 2022, ransomware payments too: After several years of sustained "growth," 2022 was the first time that the volume of cryptocurrency transactions linked to criminal activity saw a decline (they actually went up, but if we remove the sanctions category, which is more of a gray area, they went down).
Several categories, such as ransomware, scams, darknet markets, financial fraud shops, cybercrime activities, terrorist funding, and CSAM and& human trafficking, saw a year-over-year decline compared to 2021, according to a recent report from blockchain analysis company Chainalysis. (more on Risky Biz News).




